Encryption Technology
KEY TAKEAWAYS
- Strong encryption is essential to the secure operation of public and private sector services, such as banking, medical records, military communications, and the national power grid.
- Encryption also is used by criminals to hide their activities and identity from law enforcement.
- The Fourth Amendment to the Constitution strikes a balance between the individual citizen’s reasonable expectation of privacy and the legitimate need for the government to investigate criminal activity, including by gaining access to the most intimate spaces in people’s lives, such as the home.
Encryption, a process to secure information from unwanted access, has been a part of the human record since at least the time of the ancient Greeks. Thomas Jefferson invented a wheel cipher that the Navy recreated and used during World War II. More recently, mathematical formulas and advanced computing power have enabled much more secure means of encrypting communications and data.
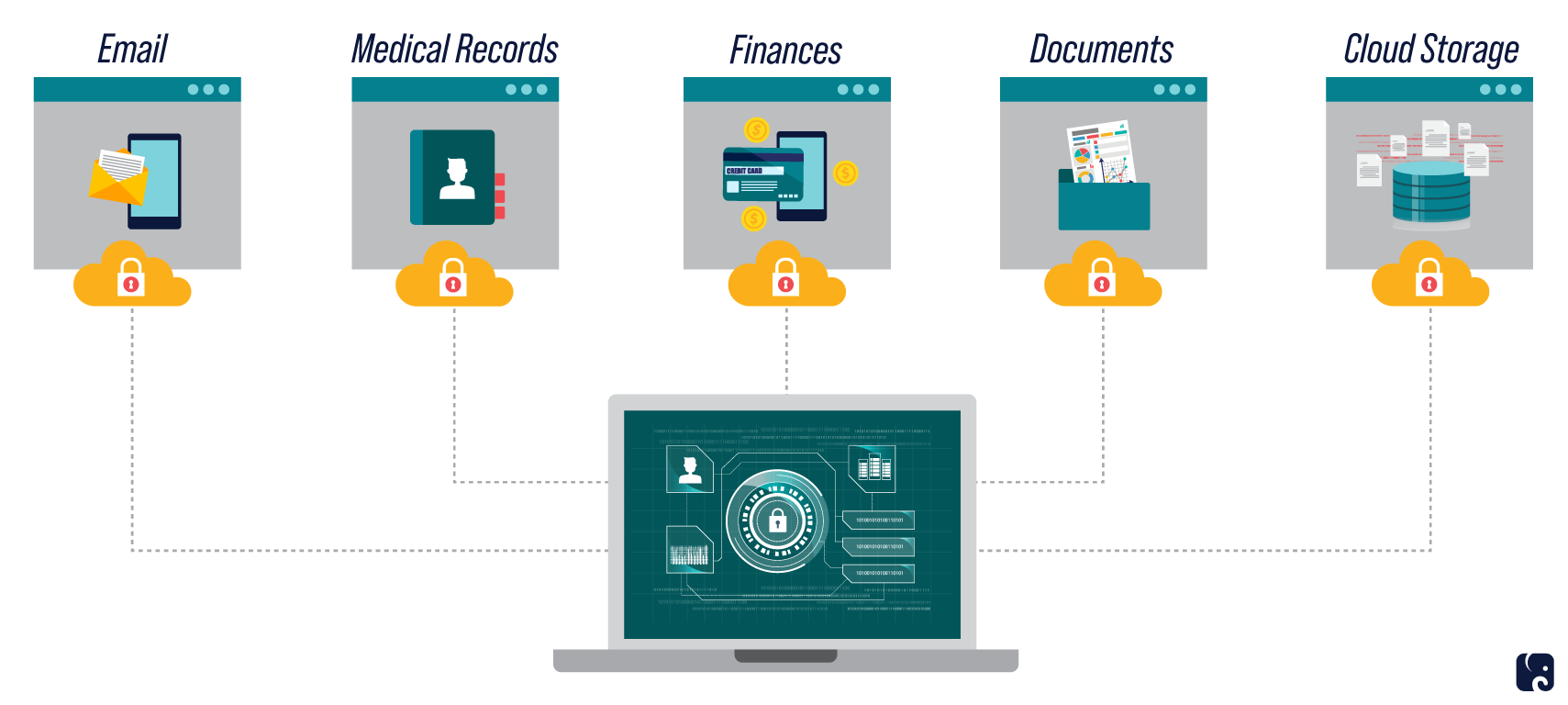
The process of encryption underpins the modern internet and is critical to nearly every part of the American economy and national security. It is essential to the security of banking, medical records, military communications, and the power grid.
How Encryption Works

How it works
At its simplest, encryption changes information that can be read into information that cannot be read. Decryption uses the same technology to change the information back to readable text. There are a wide variety of encryption methods, or standards, publicly available for anyone to use, including a popular version developed by the National Institute of Standards and Technology.
The encryption process uses keys to keep data secure. Just as a house key unlocks the door for anyone who has the key, anyone who has access to the encryption key has access to the data. For this reason, modern systems go to great lengths to ensure the keys are secure. In Apple’s iPhone system, the decryption key is generated by a combination of the passcode users create and each phone’s unique identifier. The key is not stored on the device, and outsiders, including Apple, do not have access to the key, so they are unable to decrypt the data without the user’s passcode.
Most modern systems increase security by using a different key for encrypting data and for decrypting it. They also use both “public” and “private” keys. Public keys are not secret. They are held by trusted third parties, but anyone can use them to encrypt data. However, the data can only be decrypted with a private key, which is secret. One advantage of this system is that the sender and receiver never need to send copies of their keys to each other, thus eliminating the chance they could be intercepted and the security of the messages compromised. This also allows many users to communicate with one another securely.
Encryption Is Used in a Wide Variety of Services
importance to the national Economy
Strong encryption protects the emails, text messages, personal photos, finances, online transactions, and health, location, and other sensitive data of nearly all Americans. As the coronavirus pandemic accelerates the trend of American life and commerce moving online, the importance of security online only increases. Most smartphones use passcodes and other encryption methods to help accomplish this.
The internet itself relies on people having confidence that their communication and transactions online are secure. The locked padlock emblem displayed in a web browser’s address bar indicates that the site is secured by encryption. Websites without this emblem leave users’ data exposed and should be avoided.
Fourth amendment considerations
The Fourth Amendment to the Constitution strikes a balance between the individual citizen’s reasonable expectation of privacy and the legitimate need for the government to investigate criminal activity. This includes gaining access to the most intimate spaces in people’s lives, such as the home. Given the basic responsibility of government to protect the safety of its citizens, the Fourth Amendment provides for a process to gain access to any person’s private space. There is no exception for data protected by encryption. The government must first establish probable cause to believe that a criminal offense has been committed and that there is a fair probability that evidence of the crime can be found in that place. Probable cause is decided by a judge who is a neutral decision-maker independent of the law enforcement agency seeking the warrant.
the “going dark” debate
While encryption protects essential activity in American society and our economy, it is also easily exploited by criminals. Encrypted communications can make it difficult – potentially impossible – to investigate and prosecute serious crimes like rape, murder, and terrorism. The term “going dark” is used to describe the inability of law enforcement to access data because of strong encryption. Law enforcement groups argue that strong encryption and lawful access are not binary choices, and creating “lawful access” capabilities does not necessarily mean removing encryption altogether. Some contend that, although these capabilities may weaken the overall security of a device or system, the significant benefits of protecting the public from terrorists and criminal actors can outweigh that reduced security. Cybersecurity experts and privacy advocates counter the potential benefits would not outweigh the risks and that weakening encryption, even in legitimate attempts to assist law enforcement, would harm the privacy and security of millions of law-abiding American citizens and companies.
The debate received intense media and congressional scrutiny in 2016, after Syed Rizwan Farook and Tashfeen Malik carried out a terrorist mass shooting and attempted bombing in San Bernardino, California, ultimately killing 14 people and seriously wounding 22 others. Farook and Malik fled the scene and were killed later in a shootout with police. Before they died, they both destroyed their personal phones. The FBI was able to obtain Farook’s work phone intact but were unable to unlock it. A federal magistrate judge ordered Apple to provide “reasonable technical assistance” to the FBI in obtaining access to the contents of the phone. Apple contended the order would require it to write special code that would be a master key that could unlock any iPhone. If the FBI could get access, Apple argued, so could anyone else – there was no way to create a backdoor just for the good guys. Apple resisted the court order, and ultimately the FBI got into the device by paying outside hackers an estimated $1.3 million to gain access to the data. The hackers exploited a previously unknown software flaw to bypass the encryption protections. This model – spending millions of dollars to hack into devices or systems on individual cases – is unsustainable for law enforcement entities nationwide.
Attorney General William Barr revived the debate in a July 2019 speech. He pointed out that “as we use encryption to improve cybersecurity, we must ensure that we retain society’s ability to gain lawful access to data and communications when needed to respond to criminal activity.” He also touched on the scope of criminal activity where the actors intentionally use encrypted platforms to evade detection. Examples have included:
-
Transnational drug cartels trafficking fentanyl into the United States who used the platform WhatsApp to coordinate the murders of hundreds of police officials in Mexico.
-
A 2015 terrorist attack in Garland, Texas, for which ISIS claimed responsibility and in which one terrorist exchanged approximately 100 messages with another terrorist overseas on the morning of the attack.
-
Human trafficking and child sexual exploitation cases that go undetected over internet platforms.
In the past, when technological innovation has disrupted the Fourth Amendment balance between an individual’s reasonable expectation of privacy and government’s right and obligation to investigate criminal activity, Congress and the courts have stepped in to ensure the balance is maintained. For example, Congress passed the Communications Assistance for Law Enforcement Act in 1994 to help law enforcement maintain its ability to conduct authorized electronic surveillance like wiretaps as technology evolved. CALEA requires that telecommunications providers assist law enforcement in intercepting electronic communications as long as there is a valid legal order.
On the other hand, in 2018, the Supreme Court recognized that cell phone location records gave law enforcement new means to invade privacy that were previously unimaginable. It held that accessing historical cell phone records for purposes of obtaining the location of the device constituted a search under the Fourth Amendment, and accessing them requires a probable-cause search warrant. The court noted: “As technology has enhanced the Government’s capacity to encroach upon areas normally guarded from inquisitive eyes, this Court has sought to “assure[ ] preservation of that degree of privacy against government that existed when the Fourth Amendment was adopted.”
Many of the arguments for ensuring “lawful access” to data and communications protected by encryption reference CALEA. Supporters argue end-to-end encryption is an example of a technology that has upset the Fourth Amendment balance between individual privacy rights and law enforcement’s right to investigate crimes. They say that Congress can and should step in to restore the balance, as it did with CALEA. Supporters reason that the telecom companies adapted to CALEA’s demands, and internet and smartphone companies would be able to figure out a secure and efficient way to provide access while continuing to protect data and communications. Opponents continue to insist that, because of the way encryption works, there is no way to create a backdoor for law enforcement to use that does not weaken encryption and create substantial risks for law-abiding citizens.
In an effort to bridge this divide, the Senate Judiciary Committee held a hearing in December 2019 with testimony from the Manhattan district attorney, a cybersecurity expert, and representatives from Apple and Facebook. Chairman Lindsey Graham said: “I want the average American to be protected as much as possible, but when law enforcement believes that a crime has been committed or is in the process of being committed and they get a court order, I want the government to be able to look and find out all relevant information.” Ranking Member Feinstein said that the 2015 terrorist shooting in San Bernardino influenced her position that law enforcement needed to have some way to access content when investigating major crimes.
This past June, Senators Graham, Tom Cotton, and Marsha Blackburn introduced S.4051, the Lawful Access to Encrypted Data Act. The bill mandates service providers and device manufacturers to provide assistance, following an appropriate legal process, to recover encrypted information stored on a device, operating system, remote computing service, or a wire or electronic communication service.
In recognition of the technical difficulties that have characterized this debate, the bill authorizes $50 million to encourage research into developing ways to provide law enforcement access while maximizing privacy and security. Law enforcement groups have generally expressed support for the bill, arguing it strikes an appropriate balance between security and privacy and will help protect public safety. Industry groups, privacy advocates, and security experts have generally criticized the bill. They argue that it would require companies to build backdoors into their encryption, creating vulnerabilities that could potentially expose millions of users to cyberattacks and data theft.
Next Article Previous Article